Users Love Safetica
Our customers appreciate our support, and find Safetica easy-to-use, and fast-to-implement.
Secure, manage, and monitor USB and peripheral ports to prevent unauthorized data access and mitigate the risk of data theft or loss.

Device control means setting policies and measures to oversee and manage the use of devices within an organization's network or setting. It helps keep track of who can connect to them, what data they are able to access and what actions they are allowed to perform.
Device control plays a crucial role in mitigating insider risks and protecting data within an company.
Automatically scan, identify, and classify connected external devices used by employees.
Set granular device control policies and monitor all USB ports and devices on all endpoints.

Prevent and block unauthorized device use.
Receive notifications and reports regarding USB activity on all endpoints.

Safetica enables easy and swift deployment, seamlessly integrating into existing IT infrastructure to minimize compatibility issues. Enjoy enhanced data protection and productivity without significant delays or disruptions.

Safetica’s persistent data classifications resist attempts to bypass DLP, even when files are archived, encrypted, or have a different extension. This protection extends to new documents and files leaving the protected endpoint.

Safetica offers flexible deployment options to businesses, with on-premise installation for maximum control and security, or cloud-based hosting for greater flexibility and scalability
See how Safetica can disover, classify, and protect your most valuable data through a personalized demo.
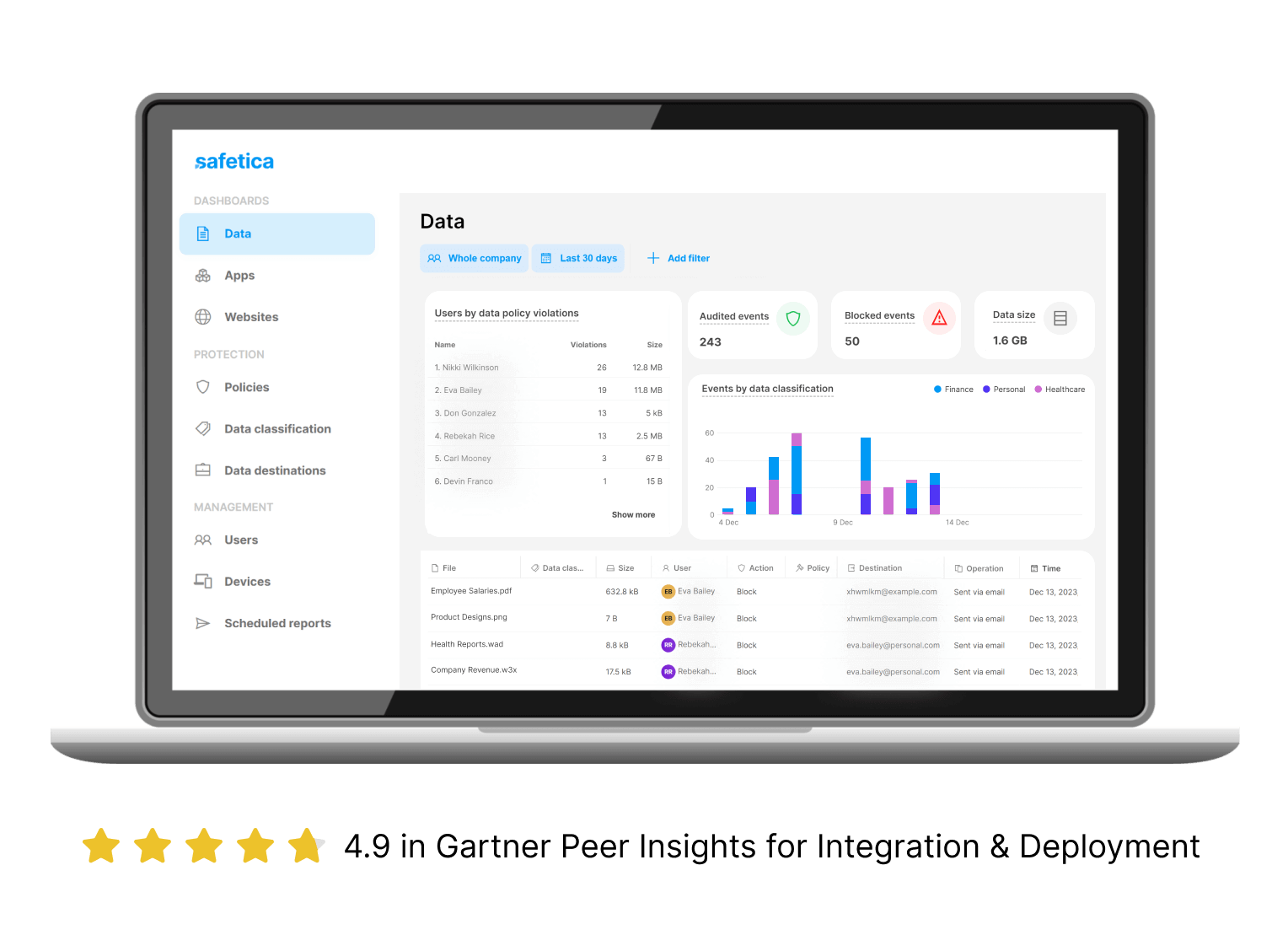
Know what sensitive data you have and where it is with DATA DISCOVERY AND DATA CLASSIFICATION
Prevent data leaks and investigate incidents with DATA LOSS PREVENTION
Proactively identify anomalous activities and detect insider threats with INSIDER RISK MANAGEMENT
Ensure compliance with data protection standards and avoid costly penalties with REGULATORY COMPLIANCE
Analyze risk in user activities and block dangerous actions with USER ACTIVITY AND WORKSPACE AUDIT
Our customers appreciate our support, and find Safetica easy-to-use, and fast-to-implement.